mirror of
https://github.com/lobehub/lobehub.git
synced 2026-03-27 13:29:15 +07:00
🐛 fix: hide password features when AUTH_DISABLE_EMAIL_PASSWORD is set (#12023)
This commit is contained in:
@@ -5,10 +5,11 @@ You are a support assistant for LobeChat authentication migration issues. Your j
|
||||
**IMPORTANT**: The official documentation website is `https://lobehub.com`. When providing documentation links, always use `https://lobehub.com/docs/...` format. Never use `lobechat.com` - that domain is incorrect.
|
||||
|
||||
Examples of correct documentation URLs:
|
||||
- `https://lobehub.com/docs/self-hosting/advanced/auth/nextauth-to-betterauth`
|
||||
- `https://lobehub.com/docs/self-hosting/advanced/auth/clerk-to-betterauth`
|
||||
- `https://lobehub.com/docs/self-hosting/advanced/auth`
|
||||
- `https://lobehub.com/docs/self-hosting/advanced/auth/providers/casdoor`
|
||||
|
||||
- `https://lobehub.com/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth`
|
||||
- `https://lobehub.com/docs/self-hosting/migration/v2/auth/clerk-to-betterauth`
|
||||
- `https://lobehub.com/docs/self-hosting/auth`
|
||||
- `https://lobehub.com/docs/self-hosting/auth/providers/casdoor`
|
||||
|
||||
## Target Issues
|
||||
|
||||
|
||||
@@ -70,12 +70,12 @@ jobs:
|
||||
```
|
||||
|
||||
2. Read the latest migration documentation based on the issue:
|
||||
- If issue #11757 (NextAuth): `cat docs/self-hosting/advanced/auth/nextauth-to-betterauth.mdx`
|
||||
- If issue #11707 (Clerk): `cat docs/self-hosting/advanced/auth/clerk-to-betterauth.mdx`
|
||||
- If issue #11757 (NextAuth): `cat docs/self-hosting/migration/v2/auth/nextauth-to-betterauth.mdx`
|
||||
- If issue #11707 (Clerk): `cat docs/self-hosting/migration/v2/auth/clerk-to-betterauth.mdx`
|
||||
|
||||
3. Read additional reference files:
|
||||
- Main auth documentation: `cat docs/self-hosting/advanced/auth.mdx`
|
||||
- Migration internals: `cat docs/self-hosting/advanced/auth/migration-internals.mdx`
|
||||
- Main auth documentation: `cat docs/self-hosting/auth.mdx`
|
||||
- Migration internals: `cat docs/self-hosting/migration/v2/auth/migration-internals.mdx`
|
||||
- Deprecated env vars checker: `cat scripts/_shared/checkDeprecatedAuth.js`
|
||||
|
||||
4. Analyze the user's comment and determine:
|
||||
|
||||
@@ -12,7 +12,7 @@ DATABASE_URL=postgresql://postgres:uWNZugjBqixf8dxC@postgresql:5432/lobechat
|
||||
AUTH_SECRET=NX2kaPE923dt6BL2U8e9oSre5RfoT7hg
|
||||
AUTH_SSO_PROVIDERS=zitadel
|
||||
# ZiTADEL provider configuration
|
||||
# Please refer to:https://lobehub.com/zh/docs/self-hosting/advanced/auth/providers/zitadel
|
||||
# Please refer to: https://lobehub.com/docs/self-hosting/auth/providers/zitadel
|
||||
AUTH_ZITADEL_ID=285945938244075523
|
||||
AUTH_ZITADEL_SECRET=hkbtzHLaCEIeHeFThym14UcydpmQiEB5JtAX08HSqSoJxhAlVVkyovTuNUZ5TNrT
|
||||
AUTH_ZITADEL_ISSUER=http://localhost:8080
|
||||
|
||||
@@ -11,7 +11,7 @@ DATABASE_URL=postgresql://postgres:uWNZugjBqixf8dxC@postgresql:5432/lobechat
|
||||
AUTH_SECRET=NX2kaPE923dt6BL2U8e9oSre5RfoT7hg
|
||||
AUTH_SSO_PROVIDERS=zitadel
|
||||
# ZiTADEL 鉴权服务提供商部分
|
||||
# 请参考:https://lobehub.com/zh/docs/self-hosting/advanced/auth/next-auth/zitadel
|
||||
# 请参考:https://lobehub.com/zh/docs/self-hosting/auth/providers/zitadel
|
||||
AUTH_ZITADEL_ID=285945938244075523
|
||||
AUTH_ZITADEL_SECRET=hkbtzHLaCEIeHeFThym14UcydpmQiEB5JtAX08HSqSoJxhAlVVkyovTuNUZ5TNrT
|
||||
AUTH_ZITADEL_ISSUER=http://localhost:8080
|
||||
|
||||
@@ -12,7 +12,7 @@ DATABASE_URL=postgresql://postgres:uWNZugjBqixf8dxC@postgresql:5432/lobe
|
||||
|
||||
# Authentication related environment variables
|
||||
# Supports Auth0, Azure AD, GitHub, Authentik, Zitadel, Logto, etc.
|
||||
# For supported providers, see: https://lobehub.com/docs/self-hosting/advanced/auth
|
||||
# For supported providers, see: https://lobehub.com/docs/self-hosting/auth
|
||||
# If you have ACCESS_CODE, please remove it. We use Better Auth as the sole authentication source
|
||||
# Required: Auth secret key. Generate with: openssl rand -base64 32
|
||||
AUTH_SECRET=NX2kaPE923dt6BL2U8e9oSre5RfoT7hg
|
||||
|
||||
@@ -11,7 +11,7 @@ DATABASE_URL=postgresql://postgres:uWNZugjBqixf8dxC@postgresql:5432/lobe
|
||||
|
||||
# 鉴权服务必需的环境变量
|
||||
# 可以使用 Auth0、Azure AD、GitHub、Authentik、Zitadel、Logto 等,如有其他接入诉求欢迎提 PR
|
||||
# 目前支持的鉴权服务提供商请参考:https://lobehub.com/zh/docs/self-hosting/advanced/auth
|
||||
# 目前支持的鉴权服务提供商请参考:https://lobehub.com/zh/docs/self-hosting/auth
|
||||
# 如果你有 ACCESS_CODE,请务必清空,我们以 Better Auth 作为唯一鉴权来源
|
||||
# 必填,用于鉴权的密钥,可以使用 openssl rand -base64 32 生成
|
||||
AUTH_SECRET=NX2kaPE923dt6BL2U8e9oSre5RfoT7hg
|
||||
|
||||
@@ -17,7 +17,7 @@ AUTH_SECRET=NX2kaPE923dt6BL2U8e9oSre5RfoT7hg
|
||||
AUTH_SSO_PROVIDERS=zitadel
|
||||
|
||||
# ZiTADEL provider configuration
|
||||
# Please refer to:https://lobehub.com/zh/docs/self-hosting/advanced/auth/providers/zitadel
|
||||
# Please refer to: https://lobehub.com/docs/self-hosting/auth/providers/zitadel
|
||||
AUTH_ZITADEL_ID=285934220675723622
|
||||
AUTH_ZITADEL_SECRET=pe7Nh3lopXkZkfqh5YEDYI2xsbIz08eZKqInOUZxssd3refRia518Apbv3DZ
|
||||
AUTH_ZITADEL_ISSUER=https://zitadel.example.com
|
||||
|
||||
@@ -16,7 +16,7 @@ AUTH_SECRET=NX2kaPE923dt6BL2U8e9oSre5RfoT7hg
|
||||
AUTH_SSO_PROVIDERS=zitadel
|
||||
|
||||
# ZiTADEL 鉴权服务提供商部分
|
||||
# 请参考:https://lobehub.com/zh/docs/self-hosting/advanced/auth/next-auth/zitadel
|
||||
# 请参考:https://lobehub.com/zh/docs/self-hosting/auth/providers/zitadel
|
||||
AUTH_ZITADEL_ID=285934220675723622
|
||||
AUTH_ZITADEL_SECRET=pe7Nh3lopXkZkfqh5YEDYI2xsbIz08eZKqInOUZxssd3refRia518Apbv3DZ
|
||||
AUTH_ZITADEL_ISSUER=https://zitadel.example.com
|
||||
|
||||
@@ -114,7 +114,7 @@ AUTH_OKTA_ISSUER: process.env.AUTH_OKTA_ISSUER,
|
||||
|
||||
### Step 4: Update Documentation (Optional)
|
||||
|
||||
Add provider documentation in `docs/self-hosting/advanced/auth.mdx` and `docs/self-hosting/advanced/auth.zh-CN.mdx`.
|
||||
Add provider documentation in `docs/self-hosting/auth.mdx` and `docs/self-hosting/auth.zh-CN.mdx`.
|
||||
|
||||
## Adding a Built-in Provider
|
||||
|
||||
|
||||
@@ -115,7 +115,7 @@ AUTH_OKTA_ISSUER: process.env.AUTH_OKTA_ISSUER,
|
||||
|
||||
### 步骤 4: 更新文档(可选)
|
||||
|
||||
在 `docs/self-hosting/advanced/auth.mdx` 和 `docs/self-hosting/advanced/auth.zh-CN.mdx` 中添加提供商文档。
|
||||
在 `docs/self-hosting/auth.mdx` 和 `docs/self-hosting/auth.zh-CN.mdx` 中添加提供商文档。
|
||||
|
||||
## 添加内置提供商
|
||||
|
||||
|
||||
@@ -10,7 +10,8 @@ tags:
|
||||
- PNPM
|
||||
- Bun
|
||||
- Git
|
||||
- VSCode
|
||||
- Docker
|
||||
- PostgreSQL
|
||||
---
|
||||
|
||||
# Environment Setup Guide
|
||||
@@ -35,6 +36,7 @@ First, you need to install the following software:
|
||||
- PNPM: We use PNPM as the preferred package manager. You can download and install it from the [PNPM official website](https://pnpm.io/installation).
|
||||
- Bun: We use Bun as the npm scripts runner. You can download and install it from the [Bun official website](https://bun.com/docs/installation).
|
||||
- Git: We use Git for version control. You can download and install it from the Git official website.
|
||||
- Docker: Required for running PostgreSQL, MinIO, and other services. You can download and install it from the [Docker official website](https://www.docker.com/get-started).
|
||||
- IDE: You can choose your preferred integrated development environment (IDE). We recommend using WebStorm/VSCode.
|
||||
|
||||
### VSCode Users
|
||||
@@ -45,20 +47,72 @@ We recommend installing the extensions listed in [.vscode/extensions.json](https
|
||||
|
||||
After installing the above software, you can start setting up the LobeHub project.
|
||||
|
||||
1. **Get the code**: First, you need to clone the LobeHub codebase from GitHub. Run the following command in the terminal:
|
||||
#### 1. Get the Code
|
||||
|
||||
First, you need to clone the LobeHub codebase from GitHub. Run the following command in the terminal:
|
||||
|
||||
```bash
|
||||
git clone https://github.com/lobehub/lobehub.git
|
||||
cd lobehub
|
||||
```
|
||||
|
||||
2. **Install dependencies**: Then, navigate to the project directory and use PNPM to install the project's dependencies:
|
||||
#### 2. Install Dependencies
|
||||
|
||||
Use PNPM to install the project's dependencies:
|
||||
|
||||
```bash
|
||||
cd lobehub
|
||||
pnpm i
|
||||
```
|
||||
|
||||
3. **Start the development server**: After installing the dependencies, you can start the development server:
|
||||
#### 3. Configure Environment
|
||||
|
||||
Copy the example environment file to create your Docker Compose configuration:
|
||||
|
||||
```bash
|
||||
cp docker-compose/local/.env.example docker-compose/local/.env
|
||||
```
|
||||
|
||||
Edit `docker-compose/local/.env` as needed for your development setup. This file contains all necessary environment variables for the Docker services and configures:
|
||||
|
||||
- **Database**: PostgreSQL with connection string
|
||||
- **Authentication**: Better Auth with Casdoor SSO
|
||||
- **Storage**: MinIO S3-compatible storage
|
||||
- **Search**: SearXNG search engine
|
||||
|
||||
#### 4. Start Docker Services
|
||||
|
||||
Start all required services using Docker Compose:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
```
|
||||
|
||||
This will start the following services:
|
||||
|
||||
- PostgreSQL database (port 5432)
|
||||
- MinIO storage (port 9000)
|
||||
- Casdoor authentication (port 8000)
|
||||
- SearXNG search (port 8080)
|
||||
|
||||
You can check all Docker services are running by running:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml ps
|
||||
```
|
||||
|
||||
#### 5. Run Database Migrations
|
||||
|
||||
Execute the database migration script to create all necessary tables:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
You should see: `✅ database migration pass.`
|
||||
|
||||
#### 6. Start Development Server
|
||||
|
||||
Launch the LobeHub development server:
|
||||
|
||||
```bash
|
||||
bun run dev
|
||||
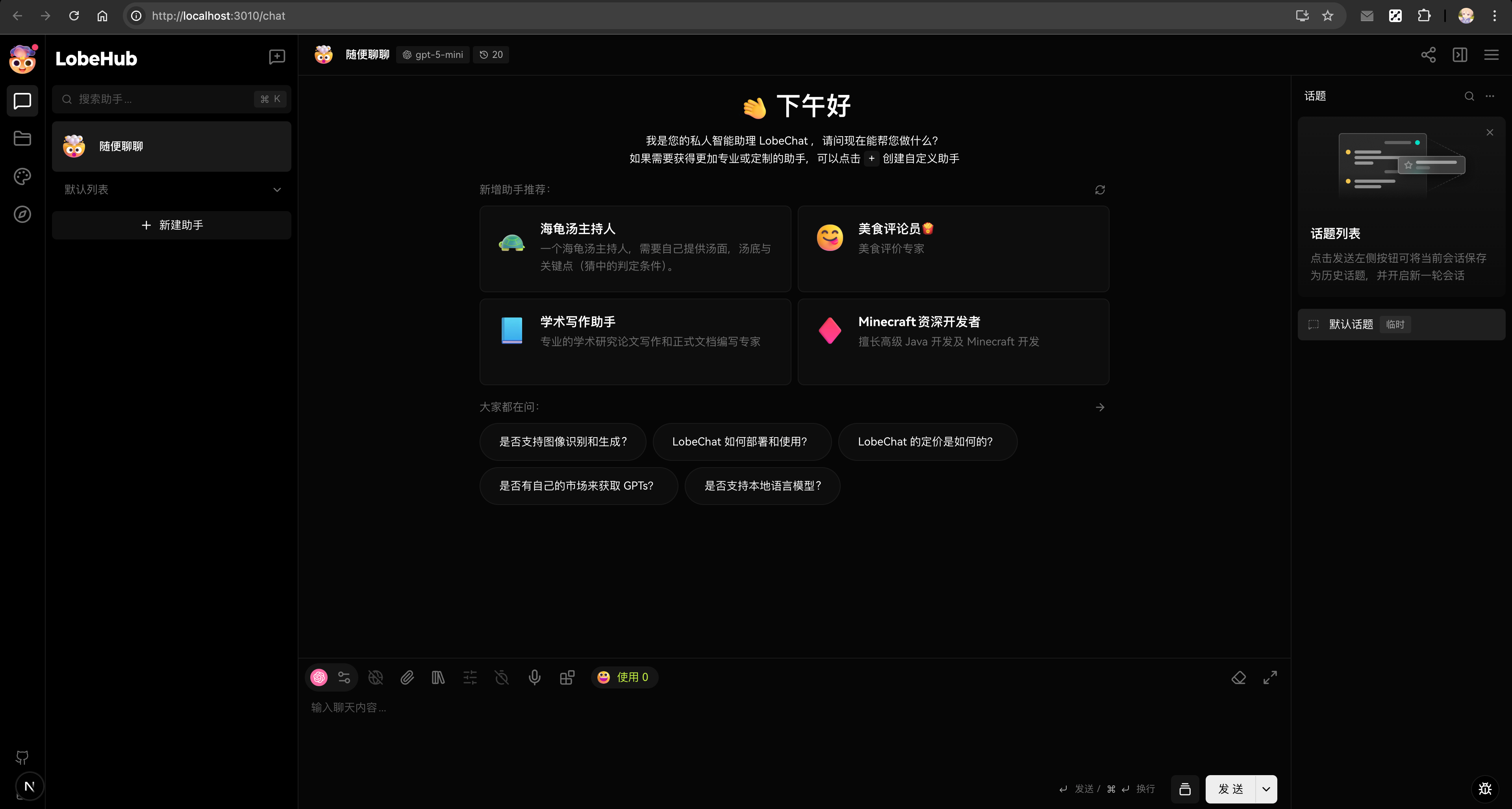
@@ -68,17 +122,125 @@ Now, you can open `http://localhost:3010` in your browser, and you should see th
|
||||
|
||||

|
||||
|
||||
## Working with Server-Side Features
|
||||
## Image Generation Development
|
||||
|
||||
The basic setup above uses LobeHub's client-side database mode. If you need to work with server-side features such as:
|
||||
When working with image generation features (text-to-image, image-to-image), the Docker Compose setup already includes all necessary storage services for handling generated images and user uploads.
|
||||
|
||||
- Database persistence
|
||||
- File uploads and storage
|
||||
- Image generation
|
||||
- Multi-user authentication
|
||||
- Advanced server-side integrations
|
||||
### Image Generation Configuration
|
||||
|
||||
Please refer to the [Work with Server-Side Database](/docs/development/basic/work-with-server-side-database) guide for complete setup instructions.
|
||||
The existing Docker Compose configuration already includes MinIO storage service and all necessary environment variables in `docker-compose/local/.env.example`. No additional setup is required.
|
||||
|
||||
### Image Generation Architecture
|
||||
|
||||
The image generation feature requires:
|
||||
|
||||
- **PostgreSQL**: Stores metadata about generated images
|
||||
- **MinIO/S3**: Stores the actual image files
|
||||
|
||||
### Storage Configuration
|
||||
|
||||
The `docker-compose/local/.env.example` file includes all necessary S3 environment variables:
|
||||
|
||||
```bash
|
||||
# S3 Storage Configuration (MinIO for local development)
|
||||
S3_ACCESS_KEY_ID=${MINIO_ROOT_USER}
|
||||
S3_SECRET_ACCESS_KEY=${MINIO_ROOT_PASSWORD}
|
||||
S3_ENDPOINT=http://localhost:${MINIO_PORT}
|
||||
S3_BUCKET=${MINIO_LOBE_BUCKET}
|
||||
S3_ENABLE_PATH_STYLE=1 # Required for MinIO
|
||||
S3_SET_ACL=0 # MinIO compatibility
|
||||
```
|
||||
|
||||
### File Storage Structure
|
||||
|
||||
Generated images and user uploads are organized in the MinIO bucket:
|
||||
|
||||
```
|
||||
lobe/ # S3 Bucket (MINIO_LOBE_BUCKET)
|
||||
├── generated/ # Generated images
|
||||
│ └── {userId}/
|
||||
│ └── {sessionId}/
|
||||
│ └── {imageId}.png
|
||||
└── uploads/ # User uploads for image-to-image
|
||||
└── {userId}/
|
||||
└── {fileId}.{ext}
|
||||
```
|
||||
|
||||
### Development Workflow for Images
|
||||
|
||||
When developing image generation features, generated images will be:
|
||||
|
||||
1. Created by the AI model
|
||||
2. Uploaded to S3/MinIO via presigned URLs
|
||||
3. Metadata stored in PostgreSQL
|
||||
4. Served via the public S3 URL
|
||||
|
||||
Example code for testing image upload:
|
||||
|
||||
```typescript
|
||||
// Example: Upload generated image
|
||||
const uploadUrl = await trpc.upload.createPresignedUrl.mutate({
|
||||
filename: 'generated-image.png',
|
||||
contentType: 'image/png',
|
||||
});
|
||||
|
||||
// Upload to S3
|
||||
await fetch(uploadUrl, {
|
||||
method: 'PUT',
|
||||
body: imageBlob,
|
||||
headers: { 'Content-Type': 'image/png' },
|
||||
});
|
||||
```
|
||||
|
||||
### Service URLs
|
||||
|
||||
When running with Docker Compose development setup:
|
||||
|
||||
- **PostgreSQL**: `postgres://postgres@localhost:5432/LobeHub`
|
||||
- **MinIO API**: `http://localhost:9000`
|
||||
- **MinIO Console**: `http://localhost:9001` (admin/CHANGE\_THIS\_PASSWORD\_IN\_PRODUCTION)
|
||||
- **Application**: `http://localhost:3010`
|
||||
|
||||
## Troubleshooting
|
||||
|
||||
### Reset Services
|
||||
|
||||
If you encounter issues, you can reset the entire stack:
|
||||
|
||||
```bash
|
||||
# Stop and remove all containers
|
||||
docker-compose -f docker-compose.development.yml down
|
||||
|
||||
# Remove volumes (this will delete all data)
|
||||
docker-compose -f docker-compose.development.yml down -v
|
||||
|
||||
# Start fresh
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
### Port Conflicts
|
||||
|
||||
If ports are already in use:
|
||||
|
||||
```bash
|
||||
# Check what's using the ports
|
||||
lsof -i :5432 # PostgreSQL
|
||||
lsof -i :9000 # MinIO API
|
||||
lsof -i :9001 # MinIO Console
|
||||
```
|
||||
|
||||
### Database Migrations
|
||||
|
||||
The setup script runs migrations automatically. If you need to run them manually:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
Note: In development mode with `pnpm dev:desktop`, migrations also run automatically on startup.
|
||||
|
||||
---
|
||||
|
||||
During the development process, if you encounter any issues with environment setup or have any questions about LobeHub development, feel free to ask us at any time. We look forward to seeing your contributions!
|
||||
|
||||
|
||||
@@ -7,6 +7,8 @@ tags:
|
||||
- Node.js
|
||||
- PNPM
|
||||
- Git
|
||||
- Docker
|
||||
- PostgreSQL
|
||||
---
|
||||
|
||||
# 环境设置指南
|
||||
@@ -29,8 +31,9 @@ tags:
|
||||
|
||||
- Node.js:LobeHub 是基于 Node.js 构建的,因此你需要安装 Node.js。我们建议安装最新的稳定版。
|
||||
- PNPM:我们使用 PNPM 作为管理器。你可以从 [pnpm 的官方网站](https://pnpm.io/installation) 上下载并安装。
|
||||
- Bun:我们使用 Bun 作为 npm scripts runner, 你可以从 [Bun 的官方网站](https://bun.com/docs/installation) 上下载并安装。
|
||||
- Bun:我们使用 Bun 作为 npm scripts runner,你可以从 [Bun 的官方网站](https://bun.com/docs/installation) 上下载并安装。
|
||||
- Git:我们使用 Git 进行版本控制。你可以从 Git 的官方网站上下载并安装。
|
||||
- Docker:用于运行 PostgreSQL、MinIO 等服务。你可以从 [Docker 官方网站](https://www.docker.com/get-started) 下载并安装。
|
||||
- IDE:你可以选择你喜欢的集成开发环境(IDE),我们推荐使用 WebStorm/VSCode。
|
||||
|
||||
### VSCode 用户
|
||||
@@ -41,20 +44,72 @@ tags:
|
||||
|
||||
完成上述软件的安装后,你可以开始设置 LobeHub 项目了。
|
||||
|
||||
1. **获取代码**:首先,你需要从 GitHub 上克隆 LobeHub 的代码库。在终端中运行以下命令:
|
||||
#### 1. 获取代码
|
||||
|
||||
首先,你需要从 GitHub 上克隆 LobeHub 的代码库。在终端中运行以下命令:
|
||||
|
||||
```bash
|
||||
git clone https://github.com/lobehub/lobehub.git
|
||||
cd lobehub
|
||||
```
|
||||
|
||||
2. **安装依赖**:然后,进入项目目录,并使用 `pnpm` 安装项目的依赖包:
|
||||
#### 2. 安装依赖
|
||||
|
||||
使用 PNPM 安装项目的依赖包:
|
||||
|
||||
```bash
|
||||
cd lobehub
|
||||
pnpm i
|
||||
```
|
||||
|
||||
3. **启动开发服务器**:安装完依赖后,你可以启动开发服务器:
|
||||
#### 3. 配置环境
|
||||
|
||||
复制示例环境文件来创建你的 Docker Compose 配置:
|
||||
|
||||
```bash
|
||||
cp docker-compose/local/.env.example docker-compose/local/.env
|
||||
```
|
||||
|
||||
根据需要编辑 `docker-compose/local/.env` 文件以适应你的开发设置。此文件包含 Docker 服务所需的所有环境变量,配置了:
|
||||
|
||||
- **数据库**:带连接字符串的 PostgreSQL
|
||||
- **身份验证**:带 Casdoor SSO 的 Better Auth
|
||||
- **存储**:MinIO S3 兼容存储
|
||||
- **搜索**:SearXNG 搜索引擎
|
||||
|
||||
#### 4. 启动 Docker 服务
|
||||
|
||||
使用 Docker Compose 启动所有必需的服务:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
```
|
||||
|
||||
这将启动以下服务:
|
||||
|
||||
- PostgreSQL 数据库(端口 5432)
|
||||
- MinIO 存储(端口 9000)
|
||||
- Casdoor 身份验证(端口 8000)
|
||||
- SearXNG 搜索(端口 8080)
|
||||
|
||||
可以通过运行以下命令检查所有 Docker 服务运行状态:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml ps
|
||||
```
|
||||
|
||||
#### 5. 运行数据库迁移
|
||||
|
||||
执行数据库迁移脚本以创建所有必要的表:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
预期输出:`✅ database migration pass.`
|
||||
|
||||
#### 6. 启动开发服务器
|
||||
|
||||
启动 LobeHub 开发服务器:
|
||||
|
||||
```bash
|
||||
bun run dev
|
||||
@@ -64,17 +119,125 @@ bun run dev
|
||||
|
||||
|
||||
|
||||
## 使用服务端功能
|
||||
## 图像生成开发
|
||||
|
||||
上述基础设置使用 LobeHub 的客户端数据库模式。如果你需要开发服务端功能,如:
|
||||
在开发图像生成功能(文生图、图生图)时,Docker Compose 配置已经包含了处理生成图像和用户上传所需的所有存储服务。
|
||||
|
||||
- 数据库持久化
|
||||
- 文件上传和存储
|
||||
- 图像生成
|
||||
- 多用户身份验证
|
||||
- 高级服务端集成
|
||||
### 图像生成配置
|
||||
|
||||
请参考[使用服务端数据库](/docs/development/basic/work-with-server-side-database)指南获得完整的设置说明。
|
||||
现有的 Docker Compose 配置已经包含了 MinIO 存储服务以及 `docker-compose/local/.env.example` 中的所有必要环境变量。无需额外配置。
|
||||
|
||||
### 图像生成架构
|
||||
|
||||
图像生成功能需要:
|
||||
|
||||
- **PostgreSQL**:存储生成图像的元数据
|
||||
- **MinIO/S3**:存储实际的图像文件
|
||||
|
||||
### 存储配置
|
||||
|
||||
`docker-compose/local/.env.example` 文件包含所有必要的 S3 环境变量:
|
||||
|
||||
```bash
|
||||
# S3 存储配置(本地开发使用 MinIO)
|
||||
S3_ACCESS_KEY_ID=${MINIO_ROOT_USER}
|
||||
S3_SECRET_ACCESS_KEY=${MINIO_ROOT_PASSWORD}
|
||||
S3_ENDPOINT=http://localhost:${MINIO_PORT}
|
||||
S3_BUCKET=${MINIO_LOBE_BUCKET}
|
||||
S3_ENABLE_PATH_STYLE=1 # MinIO 必需
|
||||
S3_SET_ACL=0 # MinIO 兼容性
|
||||
```
|
||||
|
||||
### 文件存储结构
|
||||
|
||||
生成的图像和用户上传在 MinIO 存储桶中按以下方式组织:
|
||||
|
||||
```
|
||||
lobe/ # S3 存储桶 (MINIO_LOBE_BUCKET)
|
||||
├── generated/ # 生成的图像
|
||||
│ └── {userId}/
|
||||
│ └── {sessionId}/
|
||||
│ └── {imageId}.png
|
||||
└── uploads/ # 用户上传的图像处理文件
|
||||
└── {userId}/
|
||||
└── {fileId}.{ext}
|
||||
```
|
||||
|
||||
### 图像开发工作流
|
||||
|
||||
在开发图像生成功能时,生成的图像将:
|
||||
|
||||
1. 由 AI 模型创建
|
||||
2. 通过预签名 URL 上传到 S3/MinIO
|
||||
3. 元数据存储在 PostgreSQL 中
|
||||
4. 通过公共 S3 URL 提供服务
|
||||
|
||||
测试图像上传的示例代码:
|
||||
|
||||
```typescript
|
||||
// 示例:上传生成的图像
|
||||
const uploadUrl = await trpc.upload.createPresignedUrl.mutate({
|
||||
filename: 'generated-image.png',
|
||||
contentType: 'image/png',
|
||||
});
|
||||
|
||||
// 上传到 S3
|
||||
await fetch(uploadUrl, {
|
||||
method: 'PUT',
|
||||
body: imageBlob,
|
||||
headers: { 'Content-Type': 'image/png' },
|
||||
});
|
||||
```
|
||||
|
||||
### 服务地址
|
||||
|
||||
运行 Docker Compose 开发环境时:
|
||||
|
||||
- **PostgreSQL**:`postgres://postgres@localhost:5432/LobeHub`
|
||||
- **MinIO API**:`http://localhost:9000`
|
||||
- **MinIO 控制台**:`http://localhost:9001` (admin/CHANGE\_THIS\_PASSWORD\_IN\_PRODUCTION)
|
||||
- **应用程序**:`http://localhost:3010`
|
||||
|
||||
## 故障排除
|
||||
|
||||
### 重置服务
|
||||
|
||||
如遇到问题,可以重置整个服务堆栈:
|
||||
|
||||
```bash
|
||||
# 停止并删除所有容器
|
||||
docker-compose -f docker-compose.development.yml down
|
||||
|
||||
# 删除卷(这将删除所有数据)
|
||||
docker-compose -f docker-compose.development.yml down -v
|
||||
|
||||
# 重新启动
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
### 端口冲突
|
||||
|
||||
如果端口已被占用:
|
||||
|
||||
```bash
|
||||
# 检查端口使用情况
|
||||
lsof -i :5432 # PostgreSQL
|
||||
lsof -i :9000 # MinIO API
|
||||
lsof -i :9001 # MinIO 控制台
|
||||
```
|
||||
|
||||
### 数据库迁移
|
||||
|
||||
配置脚本会自动运行迁移。如需手动运行:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
注意:在使用 `pnpm dev:desktop` 的开发模式下,迁移也会在启动时自动运行。
|
||||
|
||||
---
|
||||
|
||||
在开发过程中,如果你在环境设置上遇到任何问题,或者有任何关于 LobeHub 开发的问题,欢迎随时向我们提问。我们期待看到你的贡献!
|
||||
|
||||
|
||||
@@ -1,195 +0,0 @@
|
||||
---
|
||||
title: Work with Server-Side Database
|
||||
description: Learn how to set up a server-side database for LobeHub with Docker.
|
||||
tags:
|
||||
- LobeHub
|
||||
- Server-Side Database
|
||||
- Docker
|
||||
- PostgreSQL
|
||||
- MinIO
|
||||
---
|
||||
|
||||
# Work with Server-Side Database
|
||||
|
||||
LobeHub provides a battery-included experience with its client-side database.
|
||||
While some features you really care about is only available at a server-side development.
|
||||
|
||||
In order to work with the aspect of server-side database,
|
||||
you can setup all the prerequisites by following the [Deploying Server-Side Database](https://lobehub.com/docs/self-hosting/server-database) story.
|
||||
But here is the easier approach that can reduce your pain.
|
||||
|
||||
## Quick Setup
|
||||
|
||||
### Environment Configuration
|
||||
|
||||
First, copy the example environment file to create your Docker Compose configuration:
|
||||
|
||||
```bash
|
||||
cp docker-compose/local/.env.example docker-compose/local/.env
|
||||
```
|
||||
|
||||
Edit `docker-compose/local/.env` as needed for your development setup. This file contains all necessary environment variables for the Docker services and configures:
|
||||
|
||||
- **Database**: PostgreSQL with connection string
|
||||
- **Authentication**: NextAuth with Casdoor SSO
|
||||
- **Storage**: MinIO S3-compatible storage
|
||||
- **Search**: SearXNG search engine
|
||||
|
||||
### Start Docker Services
|
||||
|
||||
Start all required services using Docker Compose:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
```
|
||||
|
||||
This will start the following services:
|
||||
|
||||
- PostgreSQL database (port 5432)
|
||||
- MinIO storage (port 9000)
|
||||
- Casdoor authentication (port 8000)
|
||||
- SearXNG search (port 8080)
|
||||
|
||||
### Run Database Migrations
|
||||
|
||||
Execute the database migration script to create all necessary tables:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
You should see: `✅ database migration pass.`
|
||||
|
||||
### Start Development Server
|
||||
|
||||
Launch the LobeHub development server:
|
||||
|
||||
```bash
|
||||
pnpm dev
|
||||
```
|
||||
|
||||
The server will start on `http://localhost:3010`
|
||||
|
||||
And you can check all Docker services are running by running:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml ps
|
||||
```
|
||||
|
||||
## Image Generation Development
|
||||
|
||||
When working with image generation features (text-to-image, image-to-image), the Docker Compose setup already includes all necessary storage services for handling generated images and user uploads.
|
||||
|
||||
### Image Generation Configuration
|
||||
|
||||
The existing Docker Compose configuration already includes MinIO storage service and all necessary environment variables in `docker-compose/local/.env.example`. No additional setup is required.
|
||||
|
||||
### Image Generation Architecture
|
||||
|
||||
The image generation feature requires:
|
||||
|
||||
- **PostgreSQL**: Stores metadata about generated images
|
||||
- **MinIO/S3**: Stores the actual image files
|
||||
|
||||
### Storage Configuration
|
||||
|
||||
The `docker-compose/local/.env.example` file includes all necessary S3 environment variables:
|
||||
|
||||
```bash
|
||||
# S3 Storage Configuration (MinIO for local development)
|
||||
S3_ACCESS_KEY_ID=${MINIO_ROOT_USER}
|
||||
S3_SECRET_ACCESS_KEY=${MINIO_ROOT_PASSWORD}
|
||||
S3_ENDPOINT=http://localhost:${MINIO_PORT}
|
||||
S3_BUCKET=${MINIO_LOBE_BUCKET}
|
||||
S3_ENABLE_PATH_STYLE=1 # Required for MinIO
|
||||
S3_SET_ACL=0 # MinIO compatibility
|
||||
```
|
||||
|
||||
### File Storage Structure
|
||||
|
||||
Generated images and user uploads are organized in the MinIO bucket:
|
||||
|
||||
```
|
||||
lobe/ # S3 Bucket (MINIO_LOBE_BUCKET)
|
||||
├── generated/ # Generated images
|
||||
│ └── {userId}/
|
||||
│ └── {sessionId}/
|
||||
│ └── {imageId}.png
|
||||
└── uploads/ # User uploads for image-to-image
|
||||
└── {userId}/
|
||||
└── {fileId}.{ext}
|
||||
```
|
||||
|
||||
### Development Workflow for Images
|
||||
|
||||
When developing image generation features, generated images will be:
|
||||
|
||||
1. Created by the AI model
|
||||
2. Uploaded to S3/MinIO via presigned URLs
|
||||
3. Metadata stored in PostgreSQL
|
||||
4. Served via the public S3 URL
|
||||
|
||||
Example code for testing image upload:
|
||||
|
||||
```typescript
|
||||
// Example: Upload generated image
|
||||
const uploadUrl = await trpc.upload.createPresignedUrl.mutate({
|
||||
filename: 'generated-image.png',
|
||||
contentType: 'image/png',
|
||||
});
|
||||
|
||||
// Upload to S3
|
||||
await fetch(uploadUrl, {
|
||||
method: 'PUT',
|
||||
body: imageBlob,
|
||||
headers: { 'Content-Type': 'image/png' },
|
||||
});
|
||||
```
|
||||
|
||||
### Service URLs
|
||||
|
||||
When running with Docker Compose development setup:
|
||||
|
||||
- **PostgreSQL**: `postgres://postgres@localhost:5432/LobeHub`
|
||||
- **MinIO API**: `http://localhost:9000`
|
||||
- **MinIO Console**: `http://localhost:9001` (admin/CHANGE\_THIS\_PASSWORD\_IN\_PRODUCTION)
|
||||
- **Application**: `http://localhost:3010`
|
||||
|
||||
### Reset Services
|
||||
|
||||
If you encounter issues, you can reset the entire stack:
|
||||
|
||||
```bash
|
||||
# Stop and remove all containers
|
||||
docker-compose -f docker-compose.development.yml down
|
||||
|
||||
# Remove volumes (this will delete all data)
|
||||
docker-compose -f docker-compose.development.yml down -v
|
||||
|
||||
# Start fresh
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
### Troubleshooting
|
||||
|
||||
#### Port Conflicts
|
||||
|
||||
If ports are already in use:
|
||||
|
||||
```bash
|
||||
# Check what's using the ports
|
||||
lsof -i :5432 # PostgreSQL
|
||||
lsof -i :9000 # MinIO API
|
||||
lsof -i :9001 # MinIO Console
|
||||
```
|
||||
|
||||
#### Database Migrations
|
||||
|
||||
The setup script runs migrations automatically. If you need to run them manually:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
Note: In development mode with `pnpm dev:desktop`, migrations also run automatically on startup.
|
||||
@@ -1,195 +0,0 @@
|
||||
---
|
||||
title: 使用服务端数据库
|
||||
description: 快速设置 LobeHub 服务端数据库,支持 Docker 和图像生成。
|
||||
tags:
|
||||
- 服务端数据库
|
||||
- LobeHub
|
||||
- Docker
|
||||
- 图像生成
|
||||
- PostgreSQL
|
||||
---
|
||||
|
||||
# 使用服务端数据库
|
||||
|
||||
LobeHub 提供了内置的客户端数据库体验。
|
||||
但某些重要功能仅在服务端开发中可用。
|
||||
|
||||
为了使用服务端数据库功能,
|
||||
需要参考 [部署服务端数据库](https://lobehub.com/docs/self-hosting/server-database) 的说明来配置所有前置条件。
|
||||
本文档提供了一个更简化的配置方法,能够在本地开发时快速启动简化的服务端环境。
|
||||
|
||||
## 快速设置
|
||||
|
||||
### 环境配置
|
||||
|
||||
首先,复制示例环境文件来创建你的 Docker Compose 配置:
|
||||
|
||||
```bash
|
||||
cp docker-compose/local/.env.example docker-compose/local/.env
|
||||
```
|
||||
|
||||
根据需要编辑 `docker-compose/local/.env` 文件以适应你的开发设置。此文件包含 Docker 服务所需的所有环境变量,配置了:
|
||||
|
||||
- **数据库**: 带连接字符串的 PostgreSQL
|
||||
- **身份验证**: 带 Casdoor SSO 的 NextAuth
|
||||
- **存储**: MinIO S3 兼容存储
|
||||
- **搜索**: SearXNG 搜索引擎
|
||||
|
||||
### 启动 Docker 服务
|
||||
|
||||
使用 Docker Compose 启动所有必需的服务:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
```
|
||||
|
||||
这将启动以下服务:
|
||||
|
||||
- PostgreSQL 数据库(端口 5432)
|
||||
- MinIO 存储(端口 9000)
|
||||
- Casdoor 身份验证(端口 8000)
|
||||
- SearXNG 搜索(端口 8080)
|
||||
|
||||
### 运行数据库迁移
|
||||
|
||||
执行数据库迁移脚本以创建所有必要的表:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
预期输出:`✅ database migration pass.`
|
||||
|
||||
### 启动开发服务器
|
||||
|
||||
启动 LobeHub 开发服务器:
|
||||
|
||||
```bash
|
||||
pnpm dev
|
||||
```
|
||||
|
||||
服务器将在 `http://localhost:3010` 上启动
|
||||
|
||||
可以通过运行以下命令检查所有 Docker 服务运行状态:
|
||||
|
||||
```bash
|
||||
docker-compose -f docker-compose.development.yml ps
|
||||
```
|
||||
|
||||
## 图像生成开发
|
||||
|
||||
在开发图像生成功能(文生图、图生图)时,Docker Compose 配置已经包含了处理生成图像和用户上传所需的所有存储服务。
|
||||
|
||||
### 图像生成配置
|
||||
|
||||
现有的 Docker Compose 配置已经包含了 MinIO 存储服务以及 `docker-compose/local/.env.example` 中的所有必要环境变量。无需额外配置。
|
||||
|
||||
### 图像生成架构
|
||||
|
||||
图像生成功能需要:
|
||||
|
||||
- **PostgreSQL**:存储生成图像的元数据
|
||||
- **MinIO/S3**:存储实际的图像文件
|
||||
|
||||
### 存储配置
|
||||
|
||||
`docker-compose/local/.env.example` 文件包含所有必要的 S3 环境变量:
|
||||
|
||||
```bash
|
||||
# S3 存储配置(本地开发使用 MinIO)
|
||||
S3_ACCESS_KEY_ID=${MINIO_ROOT_USER}
|
||||
S3_SECRET_ACCESS_KEY=${MINIO_ROOT_PASSWORD}
|
||||
S3_ENDPOINT=http://localhost:${MINIO_PORT}
|
||||
S3_BUCKET=${MINIO_LOBE_BUCKET}
|
||||
S3_ENABLE_PATH_STYLE=1 # MinIO 必需
|
||||
S3_SET_ACL=0 # MinIO 兼容性
|
||||
```
|
||||
|
||||
### 文件存储结构
|
||||
|
||||
生成的图像和用户上传在 MinIO 存储桶中按以下方式组织:
|
||||
|
||||
```
|
||||
lobe/ # S3 存储桶 (MINIO_LOBE_BUCKET)
|
||||
├── generated/ # 生成的图像
|
||||
│ └── {userId}/
|
||||
│ └── {sessionId}/
|
||||
│ └── {imageId}.png
|
||||
└── uploads/ # 用户上传的图像处理文件
|
||||
└── {userId}/
|
||||
└── {fileId}.{ext}
|
||||
```
|
||||
|
||||
### 图像开发工作流
|
||||
|
||||
在开发图像生成功能时,生成的图像将:
|
||||
|
||||
1. 由 AI 模型创建
|
||||
2. 通过预签名 URL 上传到 S3/MinIO
|
||||
3. 元数据存储在 PostgreSQL 中
|
||||
4. 通过公共 S3 URL 提供服务
|
||||
|
||||
测试图像上传的示例代码:
|
||||
|
||||
```typescript
|
||||
// 示例:上传生成的图像
|
||||
const uploadUrl = await trpc.upload.createPresignedUrl.mutate({
|
||||
filename: 'generated-image.png',
|
||||
contentType: 'image/png',
|
||||
});
|
||||
|
||||
// 上传到 S3
|
||||
await fetch(uploadUrl, {
|
||||
method: 'PUT',
|
||||
body: imageBlob,
|
||||
headers: { 'Content-Type': 'image/png' },
|
||||
});
|
||||
```
|
||||
|
||||
### 服务地址
|
||||
|
||||
运行 Docker Compose 开发环境时:
|
||||
|
||||
- **PostgreSQL**:`postgres://postgres@localhost:5432/LobeHub`
|
||||
- **MinIO API**:`http://localhost:9000`
|
||||
- **MinIO 控制台**:`http://localhost:9001` (admin/CHANGE\_THIS\_PASSWORD\_IN\_PRODUCTION)
|
||||
- **应用程序**:`http://localhost:3010`
|
||||
|
||||
### 重置服务
|
||||
|
||||
如遇到问题,可以重置整个服务堆栈:
|
||||
|
||||
```bash
|
||||
# 停止并删除所有容器
|
||||
docker-compose -f docker-compose.development.yml down
|
||||
|
||||
# 删除卷(这将删除所有数据)
|
||||
docker-compose -f docker-compose.development.yml down -v
|
||||
|
||||
# 重新启动
|
||||
docker-compose -f docker-compose.development.yml up -d
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
### 故障排除
|
||||
|
||||
#### 端口冲突
|
||||
|
||||
如果端口已被占用:
|
||||
|
||||
```bash
|
||||
# 检查端口使用情况
|
||||
lsof -i :5432 # PostgreSQL
|
||||
lsof -i :9000 # MinIO API
|
||||
lsof -i :9001 # MinIO 控制台
|
||||
```
|
||||
|
||||
#### 数据库迁移
|
||||
|
||||
配置脚本会自动运行迁移。如需手动运行:
|
||||
|
||||
```bash
|
||||
pnpm db:migrate
|
||||
```
|
||||
|
||||
注意:在使用 `pnpm dev:desktop` 的开发模式下,迁移也会在启动时自动运行。
|
||||
@@ -61,41 +61,41 @@ To enable Better Auth in LobeHub, set the following environment variables:
|
||||
Click on a provider below for detailed configuration guides:
|
||||
|
||||
<Cards>
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/password'} title={'Email/Password'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/password'} title={'Email/Password'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/github'} title={'GitHub'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/github'} title={'GitHub'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/google'} title={'Google'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/google'} title={'Google'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/microsoft'} title={'Microsoft'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/microsoft'} title={'Microsoft'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/apple'} title={'Apple'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/apple'} title={'Apple'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/cognito'} title={'AWS Cognito'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/cognito'} title={'AWS Cognito'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/auth0'} title={'Auth0'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/auth0'} title={'Auth0'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/authelia'} title={'Authelia'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/authelia'} title={'Authelia'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/authentik'} title={'Authentik'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/authentik'} title={'Authentik'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/casdoor'} title={'Casdoor'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/casdoor'} title={'Casdoor'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/keycloak'} title={'Keycloak'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/keycloak'} title={'Keycloak'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/logto'} title={'Logto'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/logto'} title={'Logto'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/okta'} title={'Okta'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/okta'} title={'Okta'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/zitadel'} title={'ZITADEL'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/zitadel'} title={'ZITADEL'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/generic-oidc'} title={'Generic OIDC'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/generic-oidc'} title={'Generic OIDC'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/feishu'} title={'Feishu'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/feishu'} title={'Feishu'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/providers/wechat'} title={'WeChat'} />
|
||||
<Card href={'/docs/self-hosting/auth/providers/wechat'} title={'WeChat'} />
|
||||
</Cards>
|
||||
|
||||
## Callback URL Format
|
||||
|
||||
@@ -61,41 +61,41 @@ LobeHub 支持使用 Better Auth 配置外部身份验证服务,供企业 /
|
||||
点击下方提供商查看详细配置指南:
|
||||
|
||||
<Cards>
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/password'} title={'邮箱密码'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/password'} title={'邮箱密码'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/github'} title={'GitHub'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/github'} title={'GitHub'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/google'} title={'Google'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/google'} title={'Google'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/microsoft'} title={'Microsoft'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/microsoft'} title={'Microsoft'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/apple'} title={'Apple'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/apple'} title={'Apple'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/cognito'} title={'AWS Cognito'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/cognito'} title={'AWS Cognito'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/auth0'} title={'Auth0'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/auth0'} title={'Auth0'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/authelia'} title={'Authelia'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/authelia'} title={'Authelia'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/authentik'} title={'Authentik'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/authentik'} title={'Authentik'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/casdoor'} title={'Casdoor'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/casdoor'} title={'Casdoor'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/keycloak'} title={'Keycloak'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/keycloak'} title={'Keycloak'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/logto'} title={'Logto'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/logto'} title={'Logto'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/okta'} title={'Okta'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/okta'} title={'Okta'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/zitadel'} title={'ZITADEL'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/zitadel'} title={'ZITADEL'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/generic-oidc'} title={'Generic OIDC'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/generic-oidc'} title={'Generic OIDC'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/feishu'} title={'飞书'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/feishu'} title={'飞书'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/providers/wechat'} title={'微信'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/providers/wechat'} title={'微信'} />
|
||||
</Cards>
|
||||
|
||||
## 回调 URL 格式
|
||||
|
||||
@@ -13,7 +13,7 @@ tags:
|
||||
# Legacy Authentication
|
||||
|
||||
<Callout type={'warning'}>
|
||||
**Legacy Notice**: NextAuth and Clerk are legacy authentication methods. For new deployments, we strongly recommend using [Better Auth](/docs/self-hosting/advanced/auth) for its simplicity and flexibility.
|
||||
**Legacy Notice**: NextAuth and Clerk are legacy authentication methods. For new deployments, we strongly recommend using [Better Auth](/docs/self-hosting/auth) for its simplicity and flexibility.
|
||||
</Callout>
|
||||
|
||||
This page documents the legacy authentication methods (NextAuth and Clerk) for users who are still using these services.
|
||||
@@ -27,17 +27,17 @@ LobeHub has deeply integrated with Clerk to provide users with a secure and conv
|
||||
By setting the environment variables `NEXT_PUBLIC_CLERK_PUBLISHABLE_KEY` and `CLERK_SECRET_KEY` in LobeHub's environment, you can enable and use Clerk.
|
||||
|
||||
<Callout type={'info'}>
|
||||
For detailed Clerk configuration, see [Clerk Configuration Guide](/docs/self-hosting/advanced/auth/clerk).
|
||||
For detailed Clerk configuration, see [Clerk Configuration Guide](/docs/self-hosting/auth/clerk).
|
||||
</Callout>
|
||||
|
||||
<Callout type={'tip'}>
|
||||
To migrate from Clerk to Better Auth, see the [Clerk Migration Guide](/docs/self-hosting/advanced/auth/clerk-to-betterauth).
|
||||
To migrate from Clerk to Better Auth, see the [Clerk Migration Guide](/docs/self-hosting/migration/v2/auth/clerk-to-betterauth).
|
||||
</Callout>
|
||||
|
||||
## Next Auth
|
||||
|
||||
<Callout type={'tip'}>
|
||||
To migrate from NextAuth to Better Auth, see the [NextAuth Migration Guide](/docs/self-hosting/advanced/auth/nextauth-to-betterauth).
|
||||
To migrate from NextAuth to Better Auth, see the [NextAuth Migration Guide](/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth).
|
||||
</Callout>
|
||||
|
||||
Before using NextAuth, please set the following variables in LobeHub's environment variables:
|
||||
@@ -53,27 +53,27 @@ Before using NextAuth, please set the following variables in LobeHub's environme
|
||||
Currently supported identity verification services include:
|
||||
|
||||
<Cards>
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/auth0'} title={'Auth0'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/auth0'} title={'Auth0'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/microsoft-entra-id'} title={'Microsoft Entra ID'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/microsoft-entra-id'} title={'Microsoft Entra ID'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/authentik'} title={'Authentik'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/authentik'} title={'Authentik'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/github'} title={'Github'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/github'} title={'Github'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/zitadel'} title={'ZITADEL'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/zitadel'} title={'ZITADEL'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/authelia'} title={'Authelia'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/authelia'} title={'Authelia'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/logto'} title={'Logto'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/logto'} title={'Logto'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/keycloak'} title={'Keycloak'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/keycloak'} title={'Keycloak'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/google'} title={'Google'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/google'} title={'Google'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/next-auth/okta'} title={'Okta'} />
|
||||
<Card href={'/docs/self-hosting/auth/next-auth/okta'} title={'Okta'} />
|
||||
</Cards>
|
||||
|
||||
Click on the links to view the corresponding platform's configuration documentation.
|
||||
|
||||
@@ -11,7 +11,7 @@ tags:
|
||||
# 旧版身份验证
|
||||
|
||||
<Callout type={'warning'}>
|
||||
**旧版提示**:NextAuth 和 Clerk 是旧版身份验证方案。对于新部署,我们强烈建议使用 [Better Auth](/zh/docs/self-hosting/advanced/auth),它更简洁、更灵活。
|
||||
**旧版提示**:NextAuth 和 Clerk 是旧版身份验证方案。对于新部署,我们强烈建议使用 [Better Auth](/zh/docs/self-hosting/auth),它更简洁、更灵活。
|
||||
</Callout>
|
||||
|
||||
本页面为仍在使用这些服务的用户提供旧版身份验证方案(NextAuth 和 Clerk)的文档。
|
||||
@@ -25,17 +25,17 @@ LobeHub 与 Clerk 做了深度集成,能够为用户提供安全、便捷的
|
||||
在 LobeHub 的环境变量中设置 `NEXT_PUBLIC_CLERK_PUBLISHABLE_KEY` 和 `CLERK_SECRET_KEY`,即可开启和使用 Clerk。
|
||||
|
||||
<Callout type={'info'}>
|
||||
详细的 Clerk 配置请参阅 [Clerk 配置指南](/zh/docs/self-hosting/advanced/auth/clerk)。
|
||||
详细的 Clerk 配置请参阅 [Clerk 配置指南](/zh/docs/self-hosting/auth/clerk)。
|
||||
</Callout>
|
||||
|
||||
<Callout type={'tip'}>
|
||||
如需从 Clerk 迁移到 Better Auth,请参阅 [Clerk 迁移指南](/zh/docs/self-hosting/advanced/auth/clerk-to-betterauth)。
|
||||
如需从 Clerk 迁移到 Better Auth,请参阅 [Clerk 迁移指南](/zh/docs/self-hosting/migration/v2/auth/clerk-to-betterauth)。
|
||||
</Callout>
|
||||
|
||||
## Next Auth
|
||||
|
||||
<Callout type={'tip'}>
|
||||
如需从 NextAuth 迁移到 Better Auth,请参阅 [NextAuth 迁移指南](/zh/docs/self-hosting/advanced/auth/nextauth-to-betterauth)。
|
||||
如需从 NextAuth 迁移到 Better Auth,请参阅 [NextAuth 迁移指南](/zh/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth)。
|
||||
</Callout>
|
||||
|
||||
在使用 NextAuth 之前,请先在 LobeHub 的环境变量中设置以下变量:
|
||||
@@ -51,25 +51,25 @@ LobeHub 与 Clerk 做了深度集成,能够为用户提供安全、便捷的
|
||||
目前支持的身份验证服务有:
|
||||
|
||||
<Cards>
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/auth0'} title={'Auth0'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/auth0'} title={'Auth0'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/microsoft-entra-id'} title={'Microsoft Entra ID'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/microsoft-entra-id'} title={'Microsoft Entra ID'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/authentik'} title={'Authentik'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/authentik'} title={'Authentik'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/github'} title={'Github'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/github'} title={'Github'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/zitadel'} title={'ZITADEL'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/zitadel'} title={'ZITADEL'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/cloudflare-zero-trust'} title={'Cloudflare Zero Trust'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/authelia'} title={'Authelia'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/authelia'} title={'Authelia'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/logto'} title={'Logto'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/logto'} title={'Logto'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/keycloak'} title={'Keycloak'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/keycloak'} title={'Keycloak'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/next-auth/okta'} title={'Okta'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/next-auth/okta'} title={'Okta'} />
|
||||
</Cards>
|
||||
|
||||
点击即可查看对应平台的配置文档。
|
||||
|
||||
@@ -57,7 +57,7 @@ For small self-hosted deployments, the simplest approach is to let users reset t
|
||||
|
||||
1. **Configure Email Service**
|
||||
|
||||
Set up email service for password reset functionality. See [Email Service Configuration](/docs/self-hosting/advanced/auth#email-service-configuration).
|
||||
Set up email service for password reset functionality. See [Email Service Configuration](/docs/self-hosting/auth#email-service-configuration).
|
||||
|
||||
2. **Update Environment Variables**
|
||||
|
||||
@@ -80,7 +80,7 @@ For small self-hosted deployments, the simplest approach is to let users reset t
|
||||
```
|
||||
|
||||
<Callout type={'tip'}>
|
||||
See [Authentication Service Configuration](/docs/self-hosting/advanced/auth) for complete environment variables and SSO provider setup.
|
||||
See [Authentication Service Configuration](/docs/self-hosting/auth) for complete environment variables and SSO provider setup.
|
||||
</Callout>
|
||||
|
||||
3. **Redeploy LobeHub**
|
||||
@@ -289,7 +289,7 @@ npx tsx scripts/clerk-to-betterauth/verify.ts
|
||||
After migration is complete, follow [Simple Migration - Step 2](#steps) to configure Better Auth environment variables and redeploy.
|
||||
|
||||
<Callout type={'tip'}>
|
||||
For complete Better Auth configuration, see [Authentication Service Configuration](/docs/self-hosting/advanced/auth).
|
||||
For complete Better Auth configuration, see [Authentication Service Configuration](/docs/self-hosting/auth).
|
||||
</Callout>
|
||||
|
||||
## What Gets Migrated
|
||||
@@ -339,11 +339,11 @@ This error occurs because the database schema is outdated. Run `pnpm db:migrate`
|
||||
## Related Reading
|
||||
|
||||
<Cards>
|
||||
<Card href={'/docs/self-hosting/advanced/auth/migration-internals'} title={'Migration Technical Deep Dive'} />
|
||||
<Card href={'/docs/self-hosting/migration/v2/auth/migration-internals'} title={'Migration Technical Deep Dive'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth'} title={'Authentication Service Configuration'} />
|
||||
<Card href={'/docs/self-hosting/auth'} title={'Authentication Service Configuration'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/environment-variables/auth'} title={'Auth Environment Variables'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/legacy'} title={'Legacy Authentication (NextAuth & Clerk)'} />
|
||||
<Card href={'/docs/self-hosting/auth/legacy'} title={'Legacy Authentication (NextAuth & Clerk)'} />
|
||||
</Cards>
|
||||
|
||||
@@ -55,7 +55,7 @@ tags:
|
||||
|
||||
1. **配置邮件服务**
|
||||
|
||||
设置邮件服务以支持密码重置功能。参阅 [邮件服务配置](/zh/docs/self-hosting/advanced/auth#邮件服务配置)。
|
||||
设置邮件服务以支持密码重置功能。参阅 [邮件服务配置](/zh/docs/self-hosting/auth#邮件服务配置)。
|
||||
|
||||
2. **更新环境变量**
|
||||
|
||||
@@ -78,7 +78,7 @@ tags:
|
||||
```
|
||||
|
||||
<Callout type={'tip'}>
|
||||
查阅 [身份验证服务配置](/zh/docs/self-hosting/advanced/auth) 了解完整的环境变量和 SSO 提供商配置。
|
||||
查阅 [身份验证服务配置](/zh/docs/self-hosting/auth) 了解完整的环境变量和 SSO 提供商配置。
|
||||
</Callout>
|
||||
|
||||
3. **重新部署 LobeHub**
|
||||
@@ -283,7 +283,7 @@ npx tsx scripts/clerk-to-betterauth/verify.ts
|
||||
迁移完成后,参照 [简单迁移 - 步骤 2](#步骤) 配置 Better Auth 环境变量并重新部署。
|
||||
|
||||
<Callout type={'tip'}>
|
||||
完整的 Better Auth 配置请参阅 [身份验证服务配置](/zh/docs/self-hosting/advanced/auth),包括所有支持的 SSO 提供商和邮件服务配置。
|
||||
完整的 Better Auth 配置请参阅 [身份验证服务配置](/zh/docs/self-hosting/auth),包括所有支持的 SSO 提供商和邮件服务配置。
|
||||
</Callout>
|
||||
|
||||
## 迁移内容对比
|
||||
@@ -333,11 +333,11 @@ npx tsx scripts/clerk-to-betterauth/verify.ts
|
||||
## 相关阅读
|
||||
|
||||
<Cards>
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/migration-internals'} title={'迁移技术原理'} />
|
||||
<Card href={'/zh/docs/self-hosting/migration/v2/auth/migration-internals'} title={'迁移技术原理'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth'} title={'身份验证服务配置'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth'} title={'身份验证服务配置'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/environment-variables/auth'} title={'认证相关环境变量'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/legacy'} title={'旧版身份验证(NextAuth 和 Clerk)'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/legacy'} title={'旧版身份验证(NextAuth 和 Clerk)'} />
|
||||
</Cards>
|
||||
|
||||
@@ -15,7 +15,7 @@ tags:
|
||||
This document explains the technical principles behind authentication migration in LobeHub. It's intended for users with database and development experience who want to understand how migration works under the hood.
|
||||
|
||||
<Callout type={'info'}>
|
||||
For step-by-step migration instructions, see [NextAuth Migration](/docs/self-hosting/advanced/auth/nextauth-to-betterauth) or [Clerk Migration](/docs/self-hosting/advanced/auth/clerk-to-betterauth).
|
||||
For step-by-step migration instructions, see [NextAuth Migration](/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth) or [Clerk Migration](/docs/self-hosting/migration/v2/auth/clerk-to-betterauth).
|
||||
</Callout>
|
||||
|
||||
## Core Database Schema
|
||||
@@ -193,9 +193,9 @@ This typically happens with simple migration when logging in with a secondary em
|
||||
## Related Reading
|
||||
|
||||
<Cards>
|
||||
<Card href={'/docs/self-hosting/advanced/auth/nextauth-to-betterauth'} title={'NextAuth Migration Guide'} />
|
||||
<Card href={'/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth'} title={'NextAuth Migration Guide'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/clerk-to-betterauth'} title={'Clerk Migration Guide'} />
|
||||
<Card href={'/docs/self-hosting/migration/v2/auth/clerk-to-betterauth'} title={'Clerk Migration Guide'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth'} title={'Authentication Configuration'} />
|
||||
<Card href={'/docs/self-hosting/auth'} title={'Authentication Configuration'} />
|
||||
</Cards>
|
||||
|
||||
@@ -14,7 +14,7 @@ tags:
|
||||
本文档解释 LobeHub 认证迁移的技术原理,适合有数据库和开发经验的用户,帮助理解迁移的底层逻辑。
|
||||
|
||||
<Callout type={'info'}>
|
||||
如需分步迁移指南,请参阅 [NextAuth 迁移](/docs/self-hosting/advanced/auth/nextauth-to-betterauth) 或 [Clerk 迁移](/docs/self-hosting/advanced/auth/clerk-to-betterauth)。
|
||||
如需分步迁移指南,请参阅 [NextAuth 迁移](/zh/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth) 或 [Clerk 迁移](/zh/docs/self-hosting/migration/v2/auth/clerk-to-betterauth)。
|
||||
</Callout>
|
||||
|
||||
## 核心数据库 Schema
|
||||
@@ -192,9 +192,9 @@ tags:
|
||||
## 相关阅读
|
||||
|
||||
<Cards>
|
||||
<Card href={'/docs/self-hosting/advanced/auth/nextauth-to-betterauth'} title={'NextAuth 迁移指南'} />
|
||||
<Card href={'/zh/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth'} title={'NextAuth 迁移指南'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/clerk-to-betterauth'} title={'Clerk 迁移指南'} />
|
||||
<Card href={'/zh/docs/self-hosting/migration/v2/auth/clerk-to-betterauth'} title={'Clerk 迁移指南'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth'} title={'认证服务配置'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth'} title={'认证服务配置'} />
|
||||
</Cards>
|
||||
|
||||
@@ -133,7 +133,7 @@ For small self-hosted deployments, the simplest approach is to let users re-logi
|
||||
```
|
||||
|
||||
<Callout type={'tip'}>
|
||||
See [Authentication Service Configuration](/docs/self-hosting/advanced/auth) for complete environment variables and SSO provider setup.
|
||||
See [Authentication Service Configuration](/docs/self-hosting/auth) for complete environment variables and SSO provider setup.
|
||||
</Callout>
|
||||
|
||||
2. **Redeploy LobeHub**
|
||||
@@ -286,7 +286,7 @@ npx tsx scripts/nextauth-to-betterauth/verify.ts
|
||||
After migration is complete, follow [Simple Migration - Step 1](#steps) to configure Better Auth environment variables and redeploy.
|
||||
|
||||
<Callout type={'tip'}>
|
||||
For complete Better Auth configuration, see [Authentication Service Configuration](/docs/self-hosting/advanced/auth), including all supported SSO providers and email service configuration.
|
||||
For complete Better Auth configuration, see [Authentication Service Configuration](/docs/self-hosting/auth), including all supported SSO providers and email service configuration.
|
||||
</Callout>
|
||||
|
||||
## What Gets Migrated
|
||||
@@ -360,19 +360,19 @@ For identity providers like Casdoor or Logto, users may not have an email config
|
||||
Solution:
|
||||
|
||||
1. First configure the Webhook in LobeHub to sync user data from the identity provider:
|
||||
- [Casdoor Webhook Configuration](/docs/self-hosting/advanced/auth/providers/casdoor)
|
||||
- [Logto Webhook Configuration](/docs/self-hosting/advanced/auth/providers/logto)
|
||||
- [Casdoor Webhook Configuration](/docs/self-hosting/auth/providers/casdoor)
|
||||
- [Logto Webhook Configuration](/docs/self-hosting/auth/providers/logto)
|
||||
2. Then configure the user's email in the identity provider's admin console
|
||||
3. The user data will be synced to LobeHub via Webhook, and the user can then log in
|
||||
|
||||
## Related Reading
|
||||
|
||||
<Cards>
|
||||
<Card href={'/docs/self-hosting/advanced/auth/migration-internals'} title={'Migration Technical Deep Dive'} />
|
||||
<Card href={'/docs/self-hosting/migration/v2/auth/migration-internals'} title={'Migration Technical Deep Dive'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth'} title={'Authentication Service Configuration'} />
|
||||
<Card href={'/docs/self-hosting/auth'} title={'Authentication Service Configuration'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/environment-variables/auth'} title={'Auth Environment Variables'} />
|
||||
|
||||
<Card href={'/docs/self-hosting/advanced/auth/legacy'} title={'Legacy Authentication (NextAuth & Clerk)'} />
|
||||
<Card href={'/docs/self-hosting/auth/legacy'} title={'Legacy Authentication (NextAuth & Clerk)'} />
|
||||
</Cards>
|
||||
|
||||
@@ -130,7 +130,7 @@ Better Auth 支持更多功能,以下是新增的环境变量:
|
||||
```
|
||||
|
||||
<Callout type={'tip'}>
|
||||
查阅 [身份验证服务配置](/zh/docs/self-hosting/advanced/auth) 了解完整的环境变量和 SSO 提供商配置。
|
||||
查阅 [身份验证服务配置](/zh/docs/self-hosting/auth) 了解完整的环境变量和 SSO 提供商配置。
|
||||
</Callout>
|
||||
|
||||
2. **重新部署 LobeHub**
|
||||
@@ -282,7 +282,7 @@ npx tsx scripts/nextauth-to-betterauth/verify.ts
|
||||
迁移完成后,参照 [简单迁移 - 步骤 1](#步骤) 配置 Better Auth 环境变量并重新部署。
|
||||
|
||||
<Callout type={'tip'}>
|
||||
完整的 Better Auth 配置请参阅 [身份验证服务配置](/zh/docs/self-hosting/advanced/auth),包括所有支持的 SSO 提供商和邮件服务配置。
|
||||
完整的 Better Auth 配置请参阅 [身份验证服务配置](/zh/docs/self-hosting/auth),包括所有支持的 SSO 提供商和邮件服务配置。
|
||||
</Callout>
|
||||
|
||||
## 迁移内容对比
|
||||
@@ -356,19 +356,19 @@ npx tsx scripts/nextauth-to-betterauth/verify.ts
|
||||
解决方案:
|
||||
|
||||
1. 先在 LobeHub 中配置身份提供商的 Webhook 以同步用户数据:
|
||||
- [Casdoor Webhook 配置](/zh/docs/self-hosting/advanced/auth/providers/casdoor)
|
||||
- [Logto Webhook 配置](/zh/docs/self-hosting/advanced/auth/providers/logto)
|
||||
- [Casdoor Webhook 配置](/zh/docs/self-hosting/auth/providers/casdoor)
|
||||
- [Logto Webhook 配置](/zh/docs/self-hosting/auth/providers/logto)
|
||||
2. 然后在身份提供商的管理后台为用户配置邮箱
|
||||
3. 用户数据通过 Webhook 同步到 LobeHub 后即可正常登录
|
||||
|
||||
## 相关阅读
|
||||
|
||||
<Cards>
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/migration-internals'} title={'迁移技术原理'} />
|
||||
<Card href={'/zh/docs/self-hosting/migration/v2/auth/migration-internals'} title={'迁移技术原理'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth'} title={'身份验证服务配置'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth'} title={'身份验证服务配置'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/environment-variables/auth'} title={'认证相关环境变量'} />
|
||||
|
||||
<Card href={'/zh/docs/self-hosting/advanced/auth/legacy'} title={'旧版身份验证(NextAuth 和 Clerk)'} />
|
||||
<Card href={'/zh/docs/self-hosting/auth/legacy'} title={'旧版身份验证(NextAuth 和 Clerk)'} />
|
||||
</Cards>
|
||||
|
||||
@@ -60,11 +60,11 @@ LobeHub 2.0 only supports Better Auth authentication system. NextAuth and Clerk
|
||||
|
||||
### Migrating from NextAuth
|
||||
|
||||
See the [NextAuth Migration Guide](/docs/self-hosting/advanced/auth/nextauth-to-betterauth).
|
||||
See the [NextAuth Migration Guide](/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth).
|
||||
|
||||
### Migrating from Clerk
|
||||
|
||||
See the [Clerk Migration Guide](/docs/self-hosting/advanced/auth/clerk-to-betterauth).
|
||||
See the [Clerk Migration Guide](/docs/self-hosting/migration/v2/auth/clerk-to-betterauth).
|
||||
|
||||
## Database Mode Changes
|
||||
|
||||
|
||||
@@ -58,11 +58,11 @@ LobeHub 2.0 仅支持 Better Auth 认证系统,不再支持 NextAuth 和 Clerk
|
||||
|
||||
### 从 NextAuth 迁移
|
||||
|
||||
请参阅 [NextAuth 迁移指南](/zh/docs/self-hosting/advanced/auth/nextauth-to-betterauth)。
|
||||
请参阅 [NextAuth 迁移指南](/zh/docs/self-hosting/migration/v2/auth/nextauth-to-betterauth)。
|
||||
|
||||
### 从 Clerk 迁移
|
||||
|
||||
请参阅 [Clerk 迁移指南](/zh/docs/self-hosting/advanced/auth/clerk-to-betterauth)。
|
||||
请参阅 [Clerk 迁移指南](/zh/docs/self-hosting/migration/v2/auth/clerk-to-betterauth)。
|
||||
|
||||
## 数据库模式变更
|
||||
|
||||
|
||||
@@ -265,7 +265,7 @@ Generally, to fully run the LobeHub database version, you will need at least the
|
||||
|
||||
These services can be combined through self-hosting or online cloud services to meet various deployment needs. In this article, we provide a Docker Compose configuration entirely based on open-source self-hosted services, which can be used directly to start the LobeHub database version or modified to suit your requirements.
|
||||
|
||||
We use [RustFS](https://github.com/rustfs/rustfs) as the local S3 object storage service by default. To configure SSO authentication services, please refer to the [Authentication Services](/docs/self-hosting/advanced/auth) documentation.
|
||||
We use [RustFS](https://github.com/rustfs/rustfs) as the local S3 object storage service by default. To configure SSO authentication services, please refer to the [Authentication Services](/docs/self-hosting/auth) documentation.
|
||||
|
||||
<Callout type="warning">
|
||||
If your network topology is complex, please make sure these services can communicate properly
|
||||
@@ -350,7 +350,7 @@ If `INTERNAL_APP_URL` is not set, it defaults to `APP_URL`.
|
||||
|
||||
## Configuring Authentication
|
||||
|
||||
To configure SSO authentication services (such as Casdoor, Logto, etc.), please refer to the [Authentication Services](/docs/self-hosting/advanced/auth) documentation.
|
||||
To configure SSO authentication services (such as Casdoor, Logto, etc.), please refer to the [Authentication Services](/docs/self-hosting/auth) documentation.
|
||||
|
||||
[docker-pulls-link]: https://hub.docker.com/r/lobehub/lobehub
|
||||
[docker-pulls-shield]: https://img.shields.io/docker/pulls/lobehub/lobehub?color=45cc11&labelColor=black&style=flat-square
|
||||
|
||||
@@ -262,7 +262,7 @@ mv .env.zh-CN.example .env
|
||||
|
||||
这些服务可以通过自建或者在线云服务组合搭配,以满足不同层次的部署需求。本文中,我们提供了完全基于开源自建服务的 Docker Compose 配置,你可以直接使用这份配置文件来启动 LobeHub,也可以对之进行修改以适应你的需求。
|
||||
|
||||
我们默认使用 [RustFS](https://github.com/rustfs/rustfs) 作为本地 S3 对象存储服务。如需配置 SSO 登录鉴权服务,请参考 [身份验证服务](/zh/docs/self-hosting/advanced/auth) 文档。
|
||||
我们默认使用 [RustFS](https://github.com/rustfs/rustfs) 作为本地 S3 对象存储服务。如需配置 SSO 登录鉴权服务,请参考 [身份验证服务](/zh/docs/self-hosting/auth) 文档。
|
||||
|
||||
<Callout type="warning">
|
||||
如果你的网络拓扑较为复杂,请先确保在你的网络环境中这些服务能够正常通讯。
|
||||
@@ -346,7 +346,7 @@ environment:
|
||||
|
||||
## 配置身份验证
|
||||
|
||||
如需配置 SSO 登录鉴权服务(如 Casdoor、Logto 等),请参考 [身份验证服务](/zh/docs/self-hosting/advanced/auth) 文档。
|
||||
如需配置 SSO 登录鉴权服务(如 Casdoor、Logto 等),请参考 [身份验证服务](/zh/docs/self-hosting/auth) 文档。
|
||||
|
||||
[docker-pulls-link]: https://hub.docker.com/r/lobehub/lobehub
|
||||
[docker-pulls-shield]: https://img.shields.io/docker/pulls/lobehub/lobehub?color=45cc11&labelColor=black&style=flat-square
|
||||
|
||||
@@ -61,7 +61,7 @@ You also need to configure the `JWKS_KEY` environment variable for signing and v
|
||||
<GenerateJWKSKey />
|
||||
|
||||
<Callout type={'info'}>
|
||||
For advanced features like SSO providers, magic link login, and email verification, see [Authentication Service](/docs/self-hosting/advanced/auth).
|
||||
For advanced features like SSO providers, magic link login, and email verification, see [Authentication Service](/docs/self-hosting/auth).
|
||||
</Callout>
|
||||
|
||||
## 2. Deploying the database on Dokploy
|
||||
|
||||
@@ -62,7 +62,7 @@ S3_ENABLE_PATH_STYLE=
|
||||
<GenerateJWKSKey />
|
||||
|
||||
<Callout type={'info'}>
|
||||
如需 SSO 登录、魔法链接登录、邮箱验证等高级功能,请参阅 [身份验证服务](/zh/docs/self-hosting/advanced/auth)。
|
||||
如需 SSO 登录、魔法链接登录、邮箱验证等高级功能,请参阅 [身份验证服务](/zh/docs/self-hosting/auth)。
|
||||
</Callout>
|
||||
|
||||
## 二、在 Dokploy 上部署数据库
|
||||
|
||||
@@ -112,7 +112,7 @@ The server-side database needs to be paired with a user authentication service t
|
||||
With these variables, users can register and login with email and password.
|
||||
|
||||
<Callout type={'info'}>
|
||||
For advanced features like SSO providers, magic link login, and email verification, see [Authentication Service](/docs/self-hosting/advanced/auth).
|
||||
For advanced features like SSO providers, magic link login, and email verification, see [Authentication Service](/docs/self-hosting/auth).
|
||||
</Callout>
|
||||
</Steps>
|
||||
|
||||
|
||||
@@ -112,7 +112,7 @@ tags:
|
||||
配置这些变量后,用户即可使用邮箱和密码注册登录。
|
||||
|
||||
<Callout type={'info'}>
|
||||
如需 SSO 登录、魔法链接登录、邮箱验证等高级功能,请参阅 [身份验证服务](/zh/docs/self-hosting/advanced/auth)。
|
||||
如需 SSO 登录、魔法链接登录、邮箱验证等高级功能,请参阅 [身份验证服务](/zh/docs/self-hosting/auth)。
|
||||
</Callout>
|
||||
</Steps>
|
||||
|
||||
|
||||
@@ -66,7 +66,7 @@ Here is the process for deploying the LobeHub server database version on Zeabur:
|
||||
|
||||
Fill in those variables into your LobeHub service on Zeabur, here is a more detailed guide for [editing environment variables on Zeabur](https://zeabur.com/docs/deploy/variables).
|
||||
|
||||
For detailed configuration of Logto, refer to [this document](/docs/self-hosting/advanced/auth/providers/logto).
|
||||
For detailed configuration of Logto, refer to [this document](/docs/self-hosting/auth/providers/logto).
|
||||
|
||||
### Access your LobeHub Instance
|
||||
|
||||
|
||||
@@ -57,7 +57,7 @@ tags:
|
||||
|
||||
使用你刚绑定的域名来访问你的 Logto 控制台,创建一个新项目以获得对应的客户端 ID 与密钥,将它们填入你的 LobeHub 服务的变量中。关于如何填入变量,可以参照 [Zeabur 的官方文档](https://zeabur.com/docs/deploy/variables)。
|
||||
|
||||
Logto 的详细配置可以参考[这篇文档](/zh/docs/self-hosting/advanced/auth/providers/logto)。
|
||||
Logto 的详细配置可以参考[这篇文档](/zh/docs/self-hosting/auth/providers/logto)。
|
||||
|
||||
### 访问你的 LobeHub
|
||||
|
||||
|
||||
@@ -5,7 +5,7 @@
|
||||
* IMPORTANT: Keep this file as CommonJS (.js) for compatibility with startServer.js
|
||||
*/
|
||||
|
||||
const MIGRATION_DOC_BASE = 'https://lobehub.com/docs/self-hosting/advanced/auth';
|
||||
const MIGRATION_DOC_BASE = 'https://lobehub.com/docs/self-hosting/migration/v2/auth';
|
||||
|
||||
/**
|
||||
* Deprecated environment variable checks configuration
|
||||
|
||||
14
src/app/[variants]/(auth)/reset-password/layout.tsx
Normal file
14
src/app/[variants]/(auth)/reset-password/layout.tsx
Normal file
@@ -0,0 +1,14 @@
|
||||
import { redirect } from 'next/navigation';
|
||||
import { type PropsWithChildren } from 'react';
|
||||
|
||||
import { authEnv } from '@/envs/auth';
|
||||
|
||||
const ResetPasswordLayout = ({ children }: PropsWithChildren) => {
|
||||
if (authEnv.AUTH_DISABLE_EMAIL_PASSWORD) {
|
||||
redirect('/signin');
|
||||
}
|
||||
|
||||
return children;
|
||||
};
|
||||
|
||||
export default ResetPasswordLayout;
|
||||
@@ -59,6 +59,7 @@ const ProfileSetting = ({ mobile }: ProfileSettingProps) => {
|
||||
const isLoadedAuthProviders = useUserStore(authSelectors.isLoadedAuthProviders);
|
||||
const fetchAuthProviders = useUserStore((s) => s.fetchAuthProviders);
|
||||
const enableKlavis = useServerConfigStore(serverConfigSelectors.enableKlavis);
|
||||
const disableEmailPassword = useServerConfigStore(serverConfigSelectors.disableEmailPassword);
|
||||
const [servers, isServersInit, useFetchUserKlavisServers] = useToolStore((s) => [
|
||||
s.servers,
|
||||
s.isServersInit,
|
||||
@@ -113,7 +114,7 @@ const ProfileSetting = ({ mobile }: ProfileSettingProps) => {
|
||||
<InterestsRow mobile={mobile} />
|
||||
|
||||
{/* Password Row - For logged in users to change or set password */}
|
||||
{!isDesktop && isLogin && (
|
||||
{!isDesktop && isLogin && !disableEmailPassword && (
|
||||
<>
|
||||
<Divider style={{ margin: 0 }} />
|
||||
<PasswordRow mobile={mobile} />
|
||||
|
||||
@@ -107,6 +107,7 @@ export function defineConfig(customOptions: CustomBetterAuthOptions) {
|
||||
|
||||
emailAndPassword: {
|
||||
autoSignIn: true,
|
||||
disableSignUp: authEnv.AUTH_DISABLE_EMAIL_PASSWORD,
|
||||
enabled: !authEnv.AUTH_DISABLE_EMAIL_PASSWORD,
|
||||
maxPasswordLength: 64,
|
||||
minPasswordLength: 8,
|
||||
|
||||
Reference in New Issue
Block a user